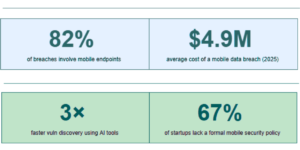
You shipped fast. You grew faster. Yet somewhere between sprint 12 and Series A, security became the thing you would “circle back to.” In an AI-first world, that is not a risk—it is a liability waiting to detonate. Mobile security testing is no longer optional; it is a survival requirement.
High-growth startups face a uniquely brutal security paradox. Your scale expands your attack surface daily, but your team focuses laser-like on product velocity. The mobile app—the face of your brand and the keeper of your users’ most sensitive data—often becomes the most neglected piece of your security posture. Therefore, mobile security testing must evolve from a one-time audit into a continuous practice.
This blog serves as your field guide. Specifically, we will cover why mobile security testing matters more than ever in the age of AI, where most startups bleed, and exactly how to build a testing practice that does not slow you down.
The AI-First World Changed Everything
AI has not just transformed how we build products—it has fundamentally shifted the threat landscape. Attackers now use AI-powered fuzzing tools that probe your API endpoints at machine speed. At the same time, they generate synthetic phishing content indistinguishable from legitimate UI. Furthermore, they can reverse-engineer obfuscated mobile binaries in hours instead of weeks.
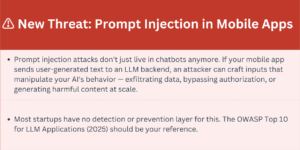
On the defensive side, your app likely ships AI features: on-device LLM inference, cloud-connected AI APIs, and personalization engines trained on user behavior. Each of these represents a new attack vector that traditional security frameworks never designed to address. Consequently, mobile security testing must now include AI-specific test cases.
The asymmetry is stark: defenders must secure every possible surface, while attackers only need to find one gap. AI amplifies attacker efficiency exponentially. Your only answer? Find and close those gaps before they do. In other words, that is the core mission of mobile security testing.
Where High-Growth Startups Actually Get Hurt
Forget the Hollywood hacker mythology. Most mobile breaches at startups are not dramatic zero-days—they are boring, preventable mistakes made at speed. Thus, here is the real threat map:
- Insecure Data Storage — Sensitive tokens, PII, and API keys hardcoded in binaries or stored in unencrypted SharedPreferences / NSUserDefaults. Attackers can extract them in minutes with basic tools on a rooted device.
- Broken API Authentication — JWT tokens with no expiry, missing signature verification, or predictable refresh logic. Mobile apps talk to APIs constantly—every endpoint is a potential entry point.
- Insufficient Transport Layer Security — Certificate pinning skipped “temporarily” during development and never re-enabled. This opens the door to man-in-the-middle attacks on public Wi-Fi, which your users absolutely use.
- Over-Permissioned SDKs — That analytics SDK you integrated in 20 minutes? It requested camera, microphone, and location access. Third-party code is untrusted code running inside your security perimeter.
- AI Model Extraction — On-device models bundled in your APK or IPA can be extracted and reverse-engineered, exposing your proprietary training data, business logic, and competitive IP.
- Deep Link Hijacking — Universal links and custom URL schemes without proper validation allow malicious apps to intercept your OAuth flows and steal authorization codes.
- Runtime Tampering — Jailbroken or rooted device detection is either missing or easily bypassed, allowing attackers to hook into your app’s runtime with tools like Frida to manipulate business logic.
“Security isn’t a feature you add at the end. It’s a tax you pay once—or a ransom you pay forever.”
OWASP Mobile Top 10 — Your North Star
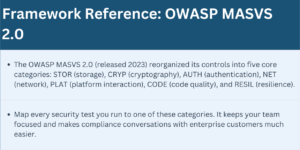
The OWASP Mobile Application Security Verification Standard (MASVS) provides the industry baseline. For startups, think of it in three tiers: L1 is the floor (basic security hygiene, non-negotiable), L2 is where you want to be before Series B, and L3 is defense-in-depth for fintech, healthtech, and enterprise. Accordingly, use mobile security testing to measure your progress against these levels.
Building a Testing Practice That Ships With You
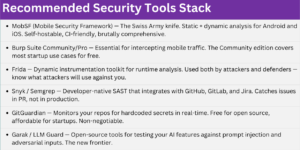
- Static Application Security Testing (SAST): Analyze your source code and compiled binaries without executing them. For mobile, this means scanning for hardcoded secrets, insecure API calls, weak cryptography, and dangerous permissions. Tools like MobSF, Semgrep, and Snyk can integrate directly into your CI pipeline—zero additional developer effort once set up.
- Dynamic Application Security Testing (DAST): Test the running application by intercepting traffic, manipulating API calls, and injecting malicious payloads. Burp Suite is the industry standard for mobile—set up an intercept proxy on your test device, install your app, and watch every API call your app makes. You will find broken authentication, missing rate limiting, and data leakage in the first session.
- Penetration Testing: Hire a specialist (or build one internally) to attack your app the way a real adversary would. This is not the same as running a scanner. A skilled pentester chains vulnerabilities together—a deeplink weakness plus an insecure API plus missing certificate pinning becomes a full account takeover. Budget for an external pentest before each major release and any fundraising round.
- AI-Specific Testing: If your app includes AI features, you need AI-specific test cases: prompt injection, model inversion attacks, adversarial inputs designed to corrupt model outputs, and data poisoning scenarios. This is a nascent discipline—the OWASP Top 10 for LLM Applications (2025) is your reference.
From Zero to Production-Grade Security
Here is the phased approach we recommend for startups at different growth stages. Each phase integrates mobile security testing deeper into your workflow.
- During Phase 1 (Pre-Product-Market Fit): focus on secrets management (no hardcoded keys), HTTPS everywhere with valid certs, basic input validation, and dependency scanning. Use free tiers of Snyk and GitGuardian. Cost: ~$0, Time: 1 sprint.
- Once you reach Seed to Series A (Phase 2): integrate SAST into CI/CD, implement certificate pinning, enable proper session management and token expiry, add root/jailbreak detection, and conduct your first internal pentest. Time: 2–3 sprints spread over a quarter.
- Between Series A and B (Phase 3): schedule an external pentest by a qualified firm, achieve OWASP MASVS L2 compliance, implement runtime application self-protection (RASP), establish a responsible disclosure program (HackerOne or Bugcrowd), and build a security champion on each squad.
- At scale (Phase 4): run red team exercises, enable continuous automated testing in production, complete a SOC 2 Type II audit, perform AI/ML-specific security reviews, and hire a dedicated AppSec engineer or team. At this stage, security becomes a competitive differentiator—enterprise customers will ask for your pentest reports before signing.
Tools That Won’t Slow Your Team Down
The best security tools are the ones your team actually uses. Here is the stack that integrates with modern startup workflows. Ultimately, effective mobile security testing relies on automation and developer-friendly tooling.
Security Is a Team Sport, Not a Gatekeeper
The biggest security failure at startups is not technical—it is cultural. When security belongs to one person (or no one), it becomes a bottleneck or a ghost. In contrast, the modern approach distributes security ownership across every engineering team through the Security Champion model.
For example, designate one engineer per squad as the security champion. They do not need to be experts—they need to be curious and empowered. Give them access to training (OWASP, TCM Security, Offensive Security), time to run security reviews before major releases, and a direct line to your CISO or senior security advisor. As a result, mobile security testing becomes a shared responsibility, not a friction point.
Your Mobile Security Testing Checklist
Run through this checklist before every major release. It captures the essentials of mobile security testing in a single page. Moreover, these items represent industry best practices.
- No hardcoded API keys, tokens, or passwords in source code or binary
- All API communication over TLS 1.2+ with valid certificate pinning
- Sensitive data encrypted at rest using platform-native secure storage (Keychain / KeyStore)
- Authentication tokens expire and are properly invalidated on logout
- App does not log sensitive data to console or crash reports in production builds
- Root / jailbreak detection implemented and tested on modified devices
- Deep links and universal links validated to prevent hijacking
- All third-party SDK permissions audited and minimized
- Dependency vulnerability scan run — no known high/critical CVEs outstanding
- OWASP MASVS L1 checklist reviewed and all items addressed or documented
- AI features tested for prompt injection with at least 20 adversarial inputs
- On-device ML models reviewed for extractability — consider encryption or server-side inference
- Rate limiting and abuse detection implemented on all auth endpoints
- Penetration test findings from last quarter reviewed and remediated
Speed and Security Are Not Enemies
The most dangerous lie in startup culture is that security slows you down. The opposite holds true: a breach slows you down catastrophically. Incident response at scale costs millions in engineering time, legal fees, regulatory fines, and customer trust—the currency you cannot buy back.
Nevertheless, the startups that get this right treat security as a product requirement, not a post-launch audit. They write threat models the same way they write product specs. They instrument their apps for security signals the same way they instrument for engagement metrics. In addition, they treat a discovered vulnerability as a shipping bug, not a PR crisis in waiting. In other words, they embed mobile security testing into every sprint.
In the AI-first world, your competitors ship features at inhuman speed with AI assistance. For this reason, your differentiation might simply be being the company that users and enterprises can actually trust. That trust is built one secure release at a time.

